Vendor Management,
Fully Under
Your Control.
One assessment. Four frameworks. Zero duplication. Your data stays in your infrastructure, always.
Built for NIS2 DORA CRA GDPR ISO 27001, implemented in accordance with ISO 31000 ISO 28001
One Assessment.
Four Frameworks.
Zero Duplication.
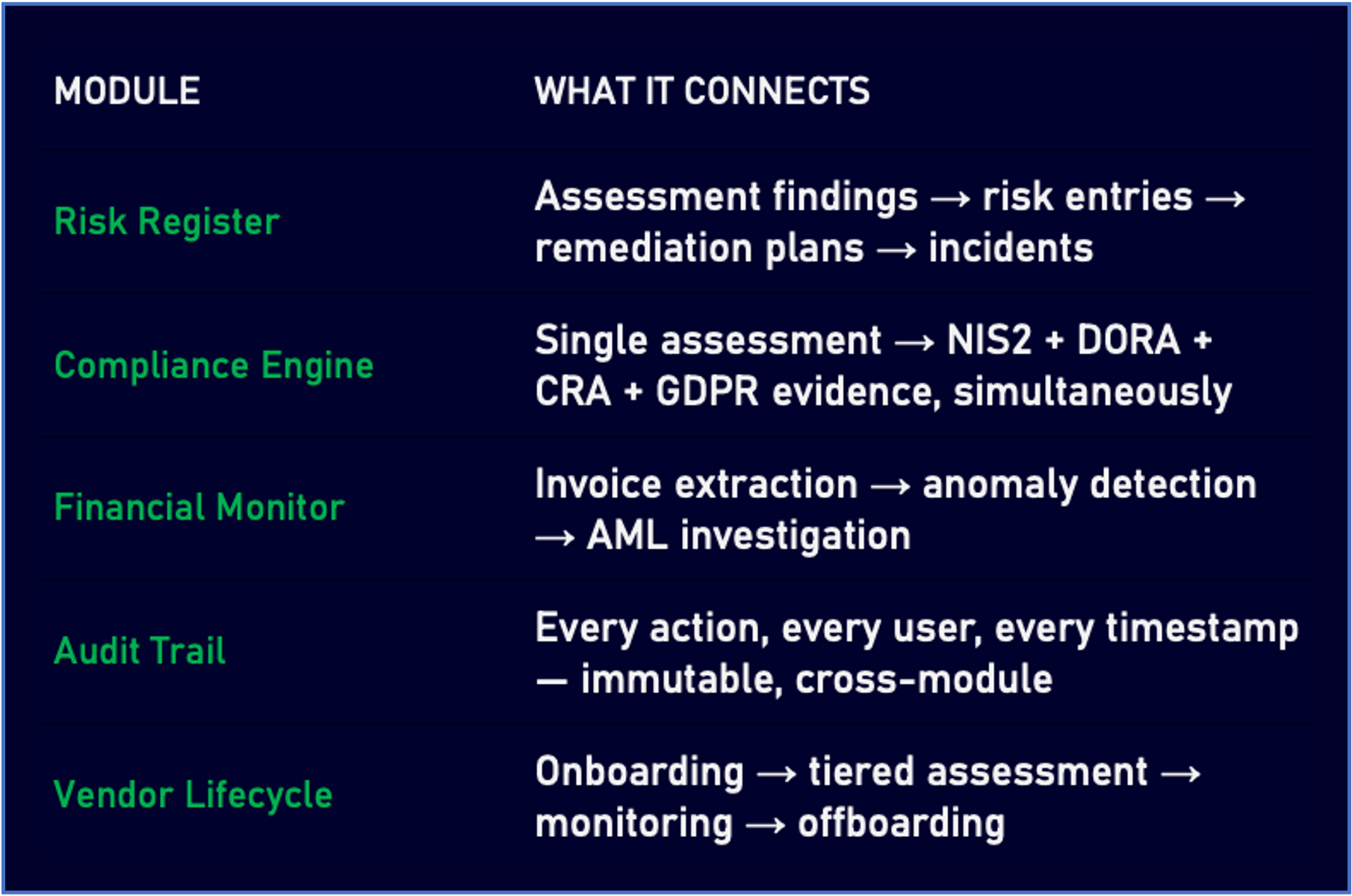
Most organisations run parallel compliance programmes against the same vendors. Njordium VIS ends that.
A single vendor assessment simultaneously maps to NIS2, DORA, CRA, GDPR, ISO 27001, implemented in accordance with ISO 31000 and ISO 28001 — out of the box. One assessment event. Seven regulatory outputs. One audit trail that satisfies all of them.
Your compliance team gets the evidence. Your auditors get the trail. Your vendors complete it once.
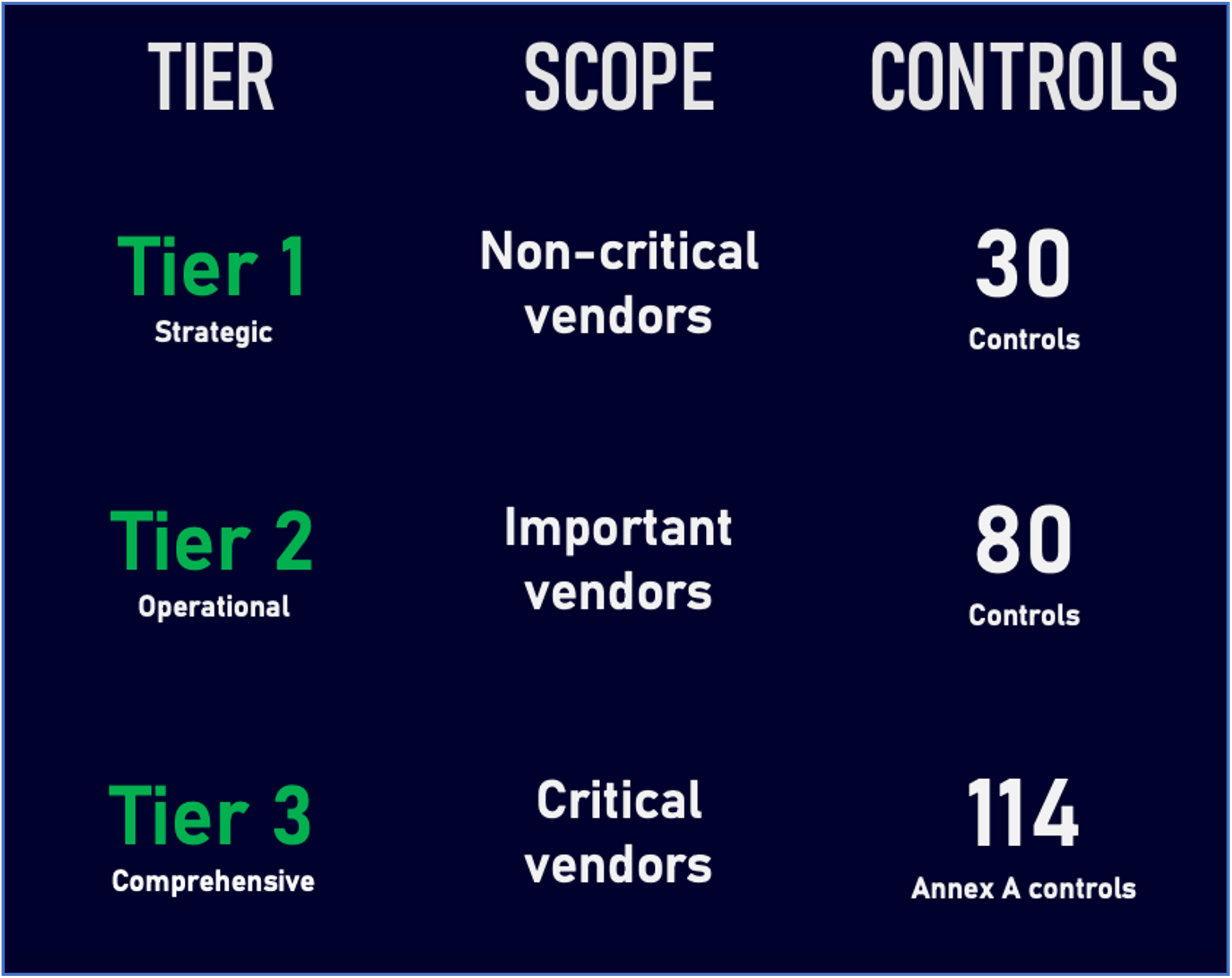
Assessment Depth Proportional to Actual Risk.
Not every vendor deserves the same scrutiny. Treating a low-risk stationery supplier the same as a critical ICT provider wastes resources and degrades programme quality.
Njordium VIS applies a three-tier model grounded in ISO 27001. Assessment effort is proportional to actual risk. Teams focus where risk is real. Vendors only answer what is relevant to their relationship with you.
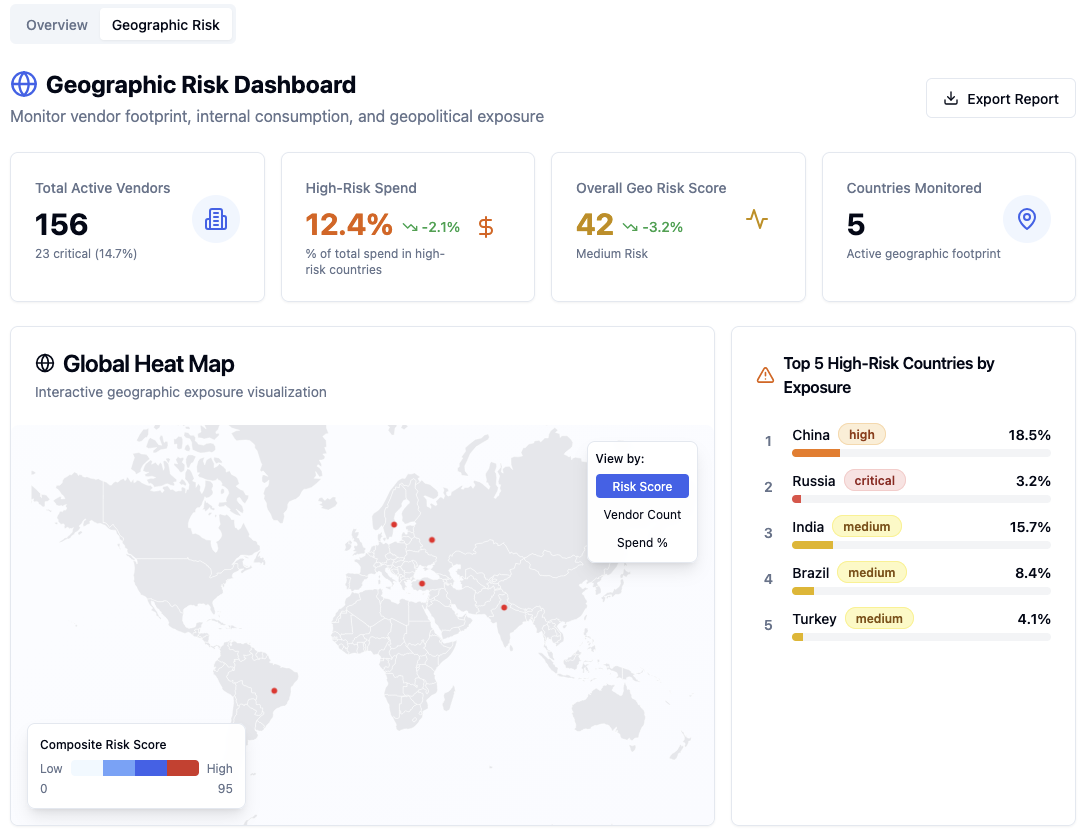
Beyond individual vendors: full Nth-party visibility — sub-vendor mapping, geographic concentration risk with heat map visualisation, and multi-tier relationship tracking with cascading compliance requirements.
AML and Vendor Risk. Finally Connected.
In most programmes, AML compliance and vendor management run in separate systems. Njordium VIS connects them.
Integrated UBO Screening
Beneficial ownership mapped and verified during onboarding, with sanctions and PEP screening, periodic re-screening, and automatic change detection. You know who you are actually doing business with before a contract is signed.
Financial Anomaly Bridge
Invoice patterns, currency transactions, and spending anomalies detected by the financial alert engine automatically feed AML investigation workflows. No manual handoff. No gap where risk falls through. Operates fully independently — no AML module required.
SAR Reporting Built In
Structured to FIU standard, with mandatory field validation, evidence attachment, and full lifecycle tracking from initial alert to case closure. The investigation starts immediately — in the same platform where the vendor relationship lives.
Your Data.
Your Infrastructure.
Full Control.
Njordium VIS deploys on-premise or in your own cloud environment. Your vendor data, risk assessments, financial records, and AML investigations never leave your infrastructure.
No black boxes.
No vendor lock-in.
No questions.
- Data stays in your infrastructure — PostgreSQL 16 as the single authoritative data model
- Immutable event log — every user action timestamped with actor identity and full context, stored in Elasticsearch
- Strict access controls — eight governance roles, each scoped precisely to their function
- Audit Observer access — read-only, cross-module visibility for internal auditors and regulators, without touching live data
- Full traceability — every AI decision, every risk score, every assessment action explained and exportable
When a regulator asks where sensitive information lives, you have the answer immediately. When an auditor requests an evidence trail, it is there in full, without reconstruction.
This is what data sovereignty looks like in practice. Not a policy statement. A verifiable architectural fact.
DORA Article 28 requires documented ICT third-party risk assessments. GDPR Article 28 requires documented processor due diligence. When these live in separate systems, the audit trail is incomplete regardless of how much assessment activity has occurred.
AI Embedded Across the Lifecycle.
Not bolted onto one task. Embedded across the entire programme — so intelligence compounds at every stage rather than disappearing after one interaction.
Intelligent Invoice Extraction
PDFs, OCR, Excel, XML, and email attachments processed automatically. The model learns from every correction, improving accuracy continuously without manual retraining. No specialist AI team required to operate it.
Self-Learning Anomaly Detection
Spending patterns, transaction behaviour, and currency flows monitored in real time. Sensitivity tunable on a 1–10 scale. False positive feedback loops refine detection continuously. Full traceability — every alert explained, every threshold visible.
Transparent Risk Scoring
JSONLogic rules, not opaque ML models. Every risk score is auditable, adjustable, and explainable to a regulator or board without specialist interpretation. No black boxes in your operations.
AI-Assisted Vendor Assessments
Assessments translated automatically into the vendor’s own language, with batch processing, language detection, caching, and quality review. Vendors complete assessments in the language they work in. Response rates go up. Cycle times come down.
Financial Crime Detection Bridge
Invoice patterns, currency transactions, and spending anomalies detected by the financial alert engine automatically feed AML investigation workflows. No manual handoff between systems. No gap where risk falls through.
Deploy today.
Demonstrate compliance tomorrow.
Pre-mapped framework domains mean your first assessment cycle produces NIS2, DORA, CRA, and GDPR evidence without custom configuration. No specialist team required. No eighteen-month implementation project.

Njord was a character in Norse mythology with the power of the (cyber) sea, the winds (trends), fishing (for intelligence), and wealth (of insights). Njordium addresses the underlying layers, rather than the (‘complex’) layer of symptoms on the surface.
Contact
Stockholm: +46 8 5078 05 06
Malmö: +46 40 686 00 46
reachout@njordium.com
